
01
Multi-Signature Escrow
All marketplace transactions are protected by a multi-signature escrow mechanism. Funds remain locked until both parties confirm order completion or a dispute moderator issues a resolution, eliminating vendor exit scams.
Informational Resource · Educational Only
An independent informational resource documenting the Nexus Darknet marketplace structure, security practices, cryptocurrency use, and operational security — compiled from open-source data for educational purposes.
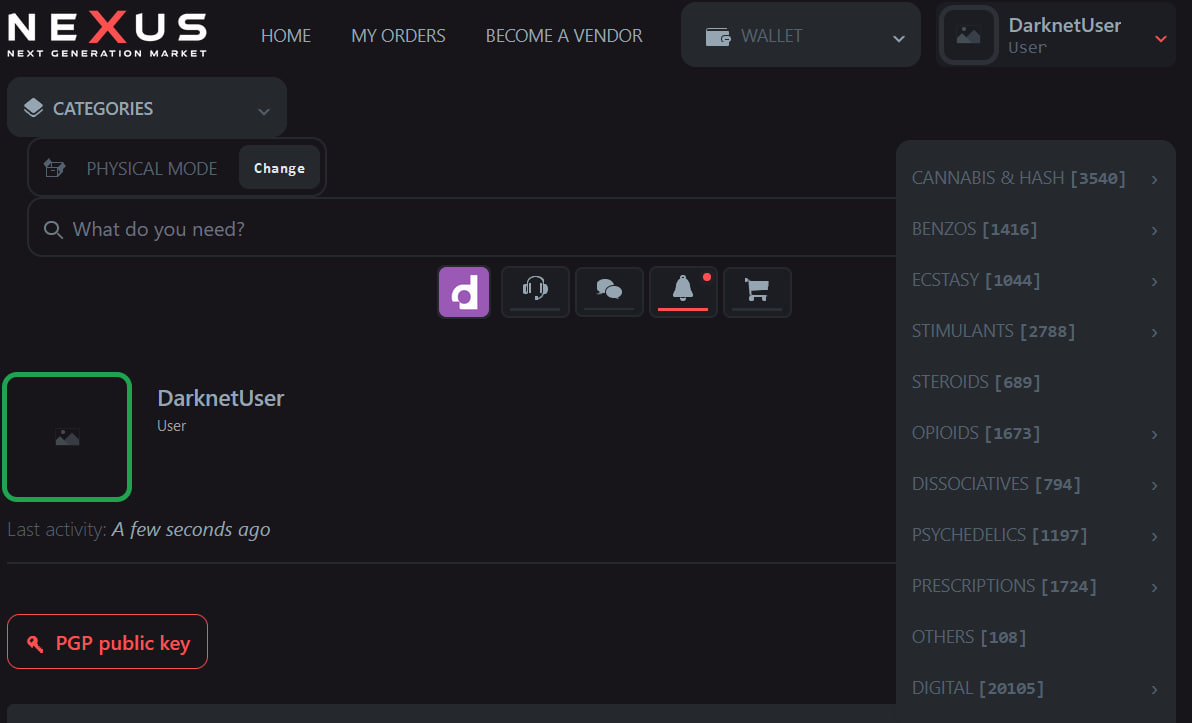
Platform Overview
The Nexus marketplace represents one of the most structured and security-conscious darknet trading platforms available on the Tor network. Operating with a strict focus on user anonymity, cryptographic verification, and transparent dispute resolution, the platform has built a reputation for reliability since its launch.
Unlike many predecessors in the darknet ecosystem, Nexus Darknet was engineered from the ground up with operational security as a core principle rather than an afterthought. The platform enforces PGP encryption on all vendor communications, requires cryptographic identity verification before vendor onboarding, and operates a fully functional escrow system to protect transaction integrity.
The architecture of the Nexus marketplace is built around the principle of minimal data retention. No JavaScript tracking, no third-party resources, no persistent identifiers — the platform strives to collect nothing that could be used to deanonymize its users.
Cryptocurrency support spans three major coins: Monero (XMR) as the privacy-native primary option, Bitcoin (BTC) for broader accessibility, and Litecoin (LTC) for fast transactions. The platform strongly incentivizes XMR use through reduced fees and faster processing, recognizing its superior privacy properties.
Core Features

01
All marketplace transactions are protected by a multi-signature escrow mechanism. Funds remain locked until both parties confirm order completion or a dispute moderator issues a resolution, eliminating vendor exit scams.
02
All communications between buyers and vendors are end-to-end encrypted using PGP. The platform enforces encryption at the protocol level, preventing plaintext message storage or interception.

03
Native integration of Monero (XMR) provides untraceable on-chain privacy. Ring signatures, stealth addresses, and RingCT technology make XMR transactions cryptographically unlinkable.
04
Vendors undergo a structured vetting process including PGP key registration, activity history review, and bond deposit. A tiered trust scoring system provides transparent vendor reputation metrics to buyers.
05
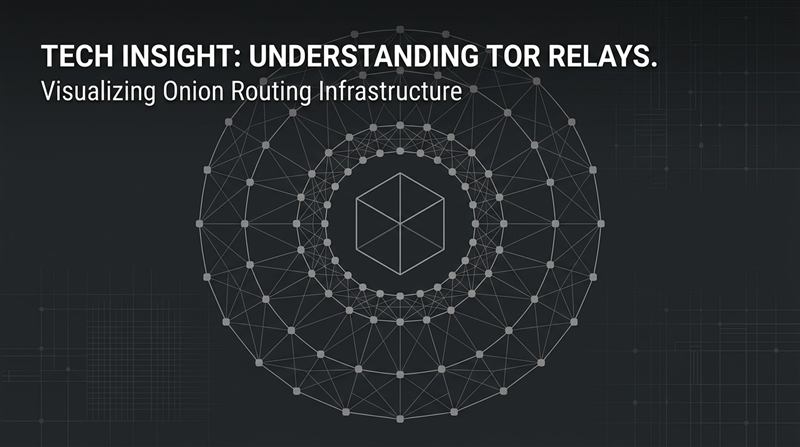
The platform exists exclusively as a Tor hidden service. There is no clearnet presence. All traffic is routed through the onion network, providing protocol-level anonymity for every connection.

06
A dedicated moderation team handles buyer-vendor disputes with clear timelines and evidence-based rulings. The transparent process includes appeal mechanisms and protects both parties' interests.
Cryptocurrency Guide
Bitcoin's 2009 launch introduced decentralized digital currency, but with a fundamental trade-off: full transaction transparency. Every transfer is permanently recorded on the public blockchain, traceable from wallet to wallet. While pseudonymous, Bitcoin has never been truly anonymous.
The rise of privacy-focused cryptocurrencies — including Monero (2014), Zcash (2016), and Dash — addressed this gap by implementing cryptographic techniques that obscure sender, receiver, and amount data at the protocol level.
Monero is the only major cryptocurrency where privacy is mandatory, not optional. Every transaction automatically uses ring signatures (obfuscates sender), stealth addresses (hides receiver), and RingCT (conceals amount). Bitcoin transactions, by contrast, leave a permanent, public, traceable record.
Operational Security
Operational security (OPSEC) is the practice of protecting critical information from adversaries. In the context of darknet operations, poor OPSEC has been the primary cause of virtually every high-profile user arrest and platform takedown. The weakest link is almost always human behavior, not technology.
Technology provides the foundation — Tor hides your network identity, encryption protects your communications, XMR obscures your financial trail — but technology alone cannot compensate for behavioral mistakes.
❌ Never reuse usernames — Using the same handle across darknet and clearnet platforms is the most common deanonymization vector.
❌ Never access via regular browser — Visiting any .onion link outside Tor Browser leaks your real IP immediately.
❌ Never share personal details — No shipping address, no real name, no phone number in any marketplace message.
❌ Never use personal devices — Work, school, or family devices may have monitoring software or logged activity.
❌ Never enable JavaScript — Malicious JS can execute code that de-anonymizes you even inside Tor Browser.
Health & Safety
Harm reduction is a set of evidence-based practices aimed at minimizing the risks associated with drug use. This information is provided for educational and safety purposes.
Always use reagent testing kits (Marquis, Mecke, Folin, Simon's) to verify substance identity and detect dangerous adulterants like fentanyl analogues before consumption.
Never take a full dose from a new batch, even from a trusted source. Product strength varies significantly. Test with a small "allergy" dose and wait for full effects before proceeding.
Have a sober, trusted person present. If alone is unavoidable, use the Never Use Alone hotline (1-800-484-3731 US) which stays on the line and calls emergency services if needed.
Some combinations are medically dangerous or fatal — particularly opioids with benzodiazepines, stimulants with MAOIs, or any depressant combination. Research TripSit's interaction chart before combining.
Naloxone (Narcan) reverses opioid overdose. Keep it accessible whenever opioids are present, even if not using opioids yourself — fentanyl contamination of other drugs is common and unpredictable.
Opioid OD: slow/stopped breathing, blue lips, unresponsive. Stimulant OD: chest pain, seizure, extreme overheating. Act immediately — call emergency services, administer naloxone for opioids.
Security Advisory
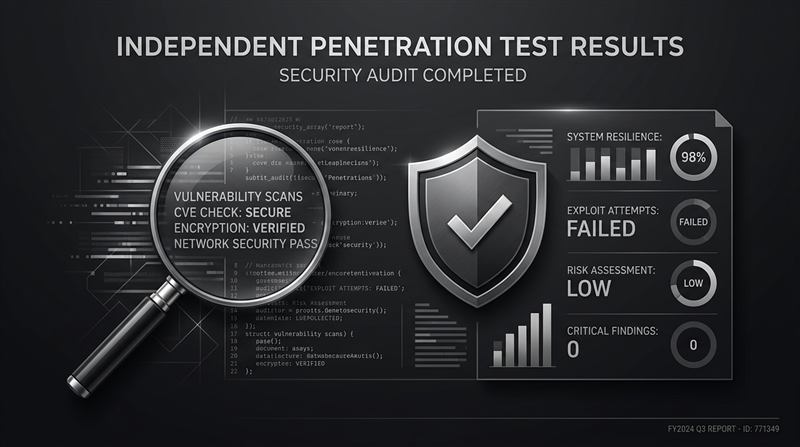
Phishing attacks targeting darknet marketplace users are widespread and sophisticated. Fake sites mimicking legitimate platforms steal login credentials and cryptocurrency. The consequences are irreversible — stolen funds cannot be recovered.
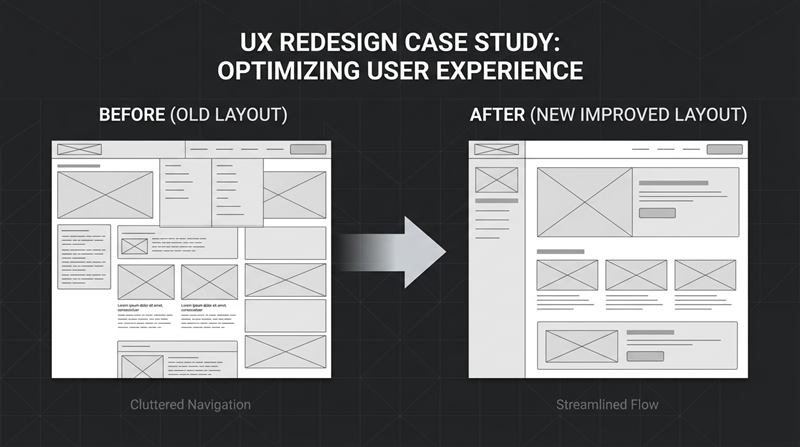
Platform Updates
Monthly security bulletin covering recent threat intelligence, platform hardening measures, and recommended user actions for the February 2026 period.
Major revision to the vendor trust scoring algorithm introduces multi-factor reliability ratings, improving buyer confidence and flagging anomalous vendor behavior patterns.

New step-by-step PGP verification workflow introduced, with improved UI and clearer key fingerprint display to help users authenticate vendor identities more reliably.

Version 2.4 of the platform search system delivers faster results, better category filtering, and improved relevance ranking based on vendor reputation and buyer feedback scores.
The Nexus development team has published a detailed 2026 roadmap covering planned security enhancements, new cryptocurrency integrations, and performance targets for the year ahead.
A comprehensive review of platform performance in 2025 — covering user growth, security audit outcomes, dispute resolution statistics, and infrastructure improvements made throughout the year.
Looking back at 2025's key milestones — from the multi-sig escrow launch to the anti-phishing campaign — this review summarizes the platform's most significant achievements.
Increased phishing activity typically accompanies holiday periods. This advisory details specific threats observed in December 2025 and provides updated guidance for staying secure.

The rollout of the native multi-signature escrow system represents a major security upgrade, eliminating centralized fund custody risks and providing cryptographic transaction protection.
Frequently Asked Questions
Questions and answers rotate daily. View the full FAQ for all entries.